dnscrypt.pl DNSSEC Outage: 2019-07-22
Date: July 22, 2019
Overview
This page gives some details on the dnscrypt.pl DNSSEC outage on July 22, 2019. This is at least the 8th DNSSEC outage for dnscrypt.pl. Please note: DNSCrypt itself is not a DNSSEC protocol and is safe to use. DNSCrypt encrypts DNS queries while DNSSEC doesn't encrypt DNS queries.
Timeline / DNSViz
- 2019-07-22 14:18:19 UTC — first personally observed dnscrypt.pl DNSSEC failure
- 2019-07-22 21:11:02 UTC — last personally observed dnscrypt.pl DNSSEC failure
Here is a mirror which shows the outage in DNSViz, courtesy of archive.is.
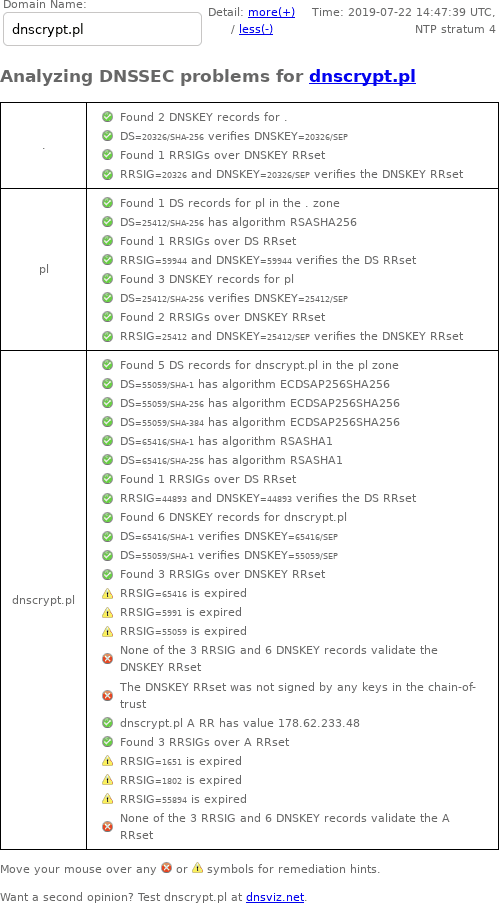
DNSSEC Debugger
Unlike DNSViz, Verisign's DNSSEC Debugger doesn't archive results, so here's a screenshot of my web browser's output from July 22, 2019:
Zonemaster
- zonemaster.iis.se archived "The apex DNSKEY RRset was not correctly signed." (mirror)
- zonemaster.net archived "The apex DNSKEY RRset was not correctly signed."
- zonemaster.labs.nic.cz archived "The apex DNSKEY RRset was not correctly signed." (mirror)
Google Public DNS, with/without DNSSEC
With DNSSEC enabled, queries fail:
$ dig +dnssec a dnscrypt.pl. @8.8.8.8
; <<>> DiG 9.4.2-P2 <<>> +dnssec a dnscrypt.pl. @8.8.8.8
;; global options: printcmd
;; Got answer:
;; ->>HEADER<<- opcode: QUERY, status: SERVFAIL, id: 36957
;; flags: qr rd ra; QUERY: 1, ANSWER: 0, AUTHORITY: 0, ADDITIONAL: 1
;; OPT PSEUDOSECTION:
; EDNS: version: 0, flags: do; udp: 512
;; QUESTION SECTION:
;dnscrypt.pl. IN A
;; Query time: 441 msec
;; SERVER: 8.8.8.8#53(8.8.8.8)
;; WHEN: Mon Jul 22 14:18:25 2019
;; MSG SIZE rcvd: 40
You have to disable DNSSEC to make DNS work:
$ dig +cd a dnscrypt.pl. @8.8.8.8
; <<>> DiG 9.4.2-P2 <<>> +cd a dnscrypt.pl. @8.8.8.8
;; global options: printcmd
;; Got answer:
;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 63335
;; flags: qr rd ra cd; QUERY: 1, ANSWER: 1, AUTHORITY: 0, ADDITIONAL: 0
;; QUESTION SECTION:
;dnscrypt.pl. IN A
;; ANSWER SECTION:
dnscrypt.pl. 59 IN A 178.62.233.48
;; Query time: 177 msec
;; SERVER: 8.8.8.8#53(8.8.8.8)
;; WHEN: Mon Jul 22 14:18:25 2019
;; MSG SIZE rcvd: 45
dns.google.com
dns.google.com is related to but separate from Google Public DNS. During this DNSSEC outage, dns.google.com showed the following for dnscrypt.pl:
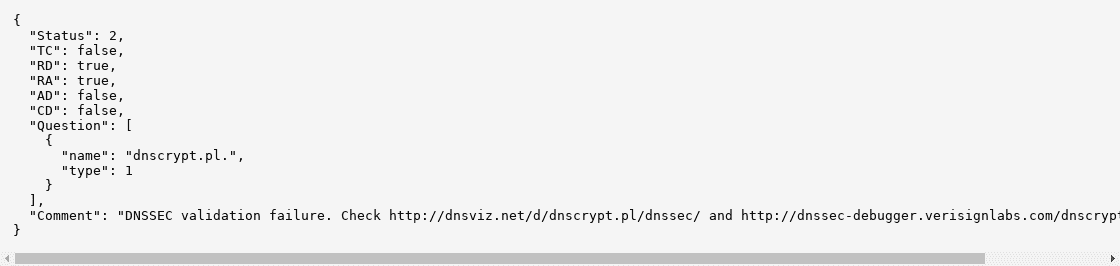
This data is also saved by archive.org.
drill trace
Since DNSSEC contains so much garbage, I put the complete drill trace into its own file, with the relevant portion below (emphasis added):
;; Domain: dnscrypt.pl.
[B] dnscrypt.pl. 86400 IN DNSKEY 257 3 13 ;{id = 55059 (ksk), size = 256b}
dnscrypt.pl. 86400 IN DNSKEY 257 3 5 ;{id = 65416 (ksk), size = 2048b}
dnscrypt.pl. 86400 IN DNSKEY 256 3 7 ;{id = 1802 (zsk), size = 1024b}
dnscrypt.pl. 86400 IN DNSKEY 256 3 5 ;{id = 1651 (zsk), size = 1024b}
dnscrypt.pl. 86400 IN DNSKEY 256 3 13 ;{id = 55894 (zsk), size = 256b}
dnscrypt.pl. 86400 IN DNSKEY 257 3 7 ;{id = 5991 (ksk), size = 2048b}
[B] dnscrypt.pl. 60 IN A 178.62.233.48
;; Error: No keys with the keytag and algorithm from the RRSIG found
;;[S] self sig OK; [B] bogus; [T] trusted
Logfile examples
- [1563805099] unbound[87354:0] info: validation failure <dnscrypt.pl. A IN>: signature expired from 79.98.145.34 for key dnscrypt.pl. while building chain of trust
- [1563829862] unbound[87354:0] info: validation failure <dnscrypt.pl. A IN>: signature expired from 193.70.13.218 for key dnscrypt.pl. while building chain of trust
