marines.mil DNSSEC Outage: 2017-05-29/30
Updated: May 30, 2017
Overview
This page gives some details on the marines.mil DNSSEC outage from May 29 to May 30, 2017.
Timeline / DNSViz
- 2017-05-29 15:37:26 UTC — www.marines.mil expired RRSIGs
- 2017-05-29 17:09:43 UTC — www.marines.mil expired RRSIGs
- 2017-05-30 00:19:55 UTC — marines.mil expired RRSIGs
- 2017-05-30 02:30:05 UTC — DNSSEC outage kind of over
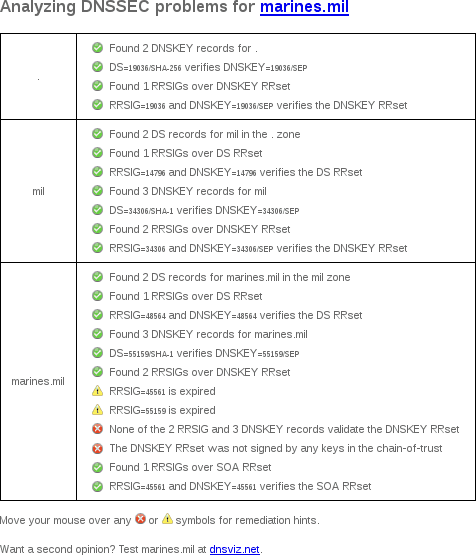
DNSSEC Debugger
Unlike DNSViz, Verisign's DNSSEC Debugger doesn't archive results, so here's a screenshot of my web browser's output from May 30, 2017.
Zonemaster
- zonemaster.net archived "Delegation from parent to child is not properly signed (signature: DNSSEC signature has expired)."
- zonemaster.fr archived "Delegation from parent to child is not properly signed (signature: DNSSEC signature has expired)."
OpenDNS & Google Public DNS
OpenDNS does not support DNSSEC, and instead supports DNSCurve. Google Public DNS currently supports only DNSSEC, and thus, Google's users saw SERVFAIL for queries under marines.mil during this outage.
With OpenDNS, without DNSSEC, queries succeed:
; <<>> DiG 9.4.2-P2 <<>> www.marines.mil. @resolver1.opendns.com.
;; global options: printcmd
;; Got answer:
;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 1263
;; flags: qr rd ra; QUERY: 1, ANSWER: 4, AUTHORITY: 0, ADDITIONAL: 0
;; QUESTION SECTION:
;www.marines.mil. IN A
;; ANSWER SECTION:
www.marines.mil. 1819 IN CNAME www.mcpw.marines.mil.edgesuite.net.
www.mcpw.marines.mil.edgesuite.net. 300 IN CNAME a1856.dscb.akamai.net.
a1856.dscb.akamai.net. 20 IN A 104.80.88.105
a1856.dscb.akamai.net. 20 IN A 104.80.88.112
;; Query time: 176 msec
;; SERVER: 208.67.222.222#53(208.67.222.222)
;; WHEN: Mon May 29 15:37:15 2017
;; MSG SIZE rcvd: 145
With Google Public DNS, because of DNSSEC, queries fail:
$ dig +dnssec www.marines.mil @8.8.8.8
; <<>> DiG 9.4.2-P2 <<>> +dnssec www.marines.mil. @8.8.8.8
;; global options: printcmd
;; Got answer:
;; ->>HEADER<<- opcode: QUERY, status: SERVFAIL, id: 9891
;; flags: qr rd ra; QUERY: 1, ANSWER: 0, AUTHORITY: 0, ADDITIONAL: 1
;; OPT PSEUDOSECTION:
; EDNS: version: 0, flags: do; udp: 512
;; QUESTION SECTION:
;www.marines.mil. IN A
;; Query time: 175 msec
;; SERVER: 8.8.8.8#53(8.8.8.8)
;; WHEN: Mon May 29 15:37:16 2017
;; MSG SIZE rcvd: 44
drill trace
Since DNSSEC contains so much garbage, I put the complete drill trace into its own file, with the relevant portion below (emphasis added):
;; Domain: marines.mil.
[B] marines.mil. 1009 IN DNSKEY 257 3 8 ;{id = 55159 (ksk), size = 2048b}
marines.mil. 1009 IN DNSKEY 256 3 8 ;{id = 48135 (zsk), size = 2048b}
marines.mil. 1009 IN DNSKEY 256 3 8 ;{id = 45561 (zsk), size = 2048b}
[B] Error verifying denial of existence for marines.mil. type A: No keys with the keytag and algorithm from the RRSIG found
;;[S] self sig OK; [B] bogus; [T] trusted
Logfile examples
- [1496077783] unbound[26477:0] info: validation failure <www.marines.mil. A IN>: signature expired for CNAME from 23.67.56.174 and 23.211.133.64 and 192.156.7.120
- [1496078790] unbound[26477:0] info: validation failure <www.marines.mil. A IN>: signature expired from 192.156.37.99 for key marines.mil. while building chain of trust
- [1496110104] unbound[26477:0] info: validation failure <www.marines.mil. A IN>: signature expired from 192.156.71.120 for key marines.mil. while building chain of trust
